Archive Request to Azure Storage Policy
Custom Policy Example
Zuplo is extensible, so we don't have a built-in policy for Archive Request to Azure Storage, instead we've a template here that shows you how you can use your superpower (code) to achieve your goals. To learn more about custom policies see the documentation.
In this example shows how you can archive the body of incoming requests to Azure Blob Storage. This can be useful for auditing, logging, or archival scenarios. Additionally, you could use this policy to save the body of a request and then enqueue some asynchronous work that uses this body.
import { HttpProblems, ZuploContext, ZuploRequest } from "@zuplo/runtime";
interface PolicyOptions {
blobContainerPath: string;
blobCreateSas: string;
}
export default async function (
request: ZuploRequest,
context: ZuploContext,
options: PolicyOptions,
policyName: string,
) {
// NOTE: policy options should be validated, but to keep the sample short,
// we are skipping that here.
// because we will read the body, we need to
// create a clone of this request first, otherwise
// there may be two attempts to read the body
// causing a runtime error
const clone = request.clone();
// In this example we assume the body could be text, but you could also
// request the blob() to handle binary data types like images.
//
// This example loads the entire body into memory. This is fine for
// small payloads, but if you have a large payload you should instead
// save the body via streaming.
const body = await clone.text();
// generate a unique blob name based on the date and requestId
const blobName = `${Date.now()}-${context.requestId}.req.txt`;
const url = `${options.blobContainerPath}/${blobName}?${options.blobCreateSas}`;
const result = await fetch(url, {
method: "PUT",
body: body,
headers: {
"x-ms-blob-type": "BlockBlob",
},
});
if (result.status > 201) {
const text = await result.text();
context.log.error("Error saving file to storage", text);
return HttpProblems.internalServerError(request, context, {
detail: text,
});
}
// continue
return request;
}tsConfiguration
The example below shows how to configure a custom code policy in the 'policies.json' document that utilizes the above example policy code.
{
"name": "my-archive-request-azure-storage-inbound-policy",
"policyType": "archive-request-azure-storage-inbound",
"handler": {
"_name": "basic",
"export": "default",
"module": "$import(./modules/YOUR_MODULE)",
"options": {
"blobCreateSas": "$env(BLOB_CREATE_SAS)",
"blobContainerPath": "$env(BLOB_CONTAINER_PATH)"
}
}
}jsonPolicy Configuration
name<string>- The name of your policy instance. This is used as a reference in your routes.policyType<string>- The identifier of the policy. This is used by the Zuplo UI. Value should bearchive-request-azure-storage-inbound.handler.export<string>- The name of the exported type. Value should bedefault.handler.module<string>- The module containing the policy. Value should be$import(./modules/YOUR_MODULE).handler.options<object>- The options for this policy. See Policy Options below.
Policy Options
The options for this policy are specified below. All properties are optional unless specifically marked as required.
blobCreateSas<string>- The Azure shared access token with permission to write to the bucketblobContainerPath<string>- The path to the Azure blob container
Using the Policy
Using the Policy
In order to use this policy, you'll need to setup Azure storage. You'll find instructions on how to do that below.
Setup Azure
First, let's set up Azure. You'll need a container in Azure storage
(docs).
Once you have your container you'll need the URL - you can get it on the
properties tab of your container as shown below.
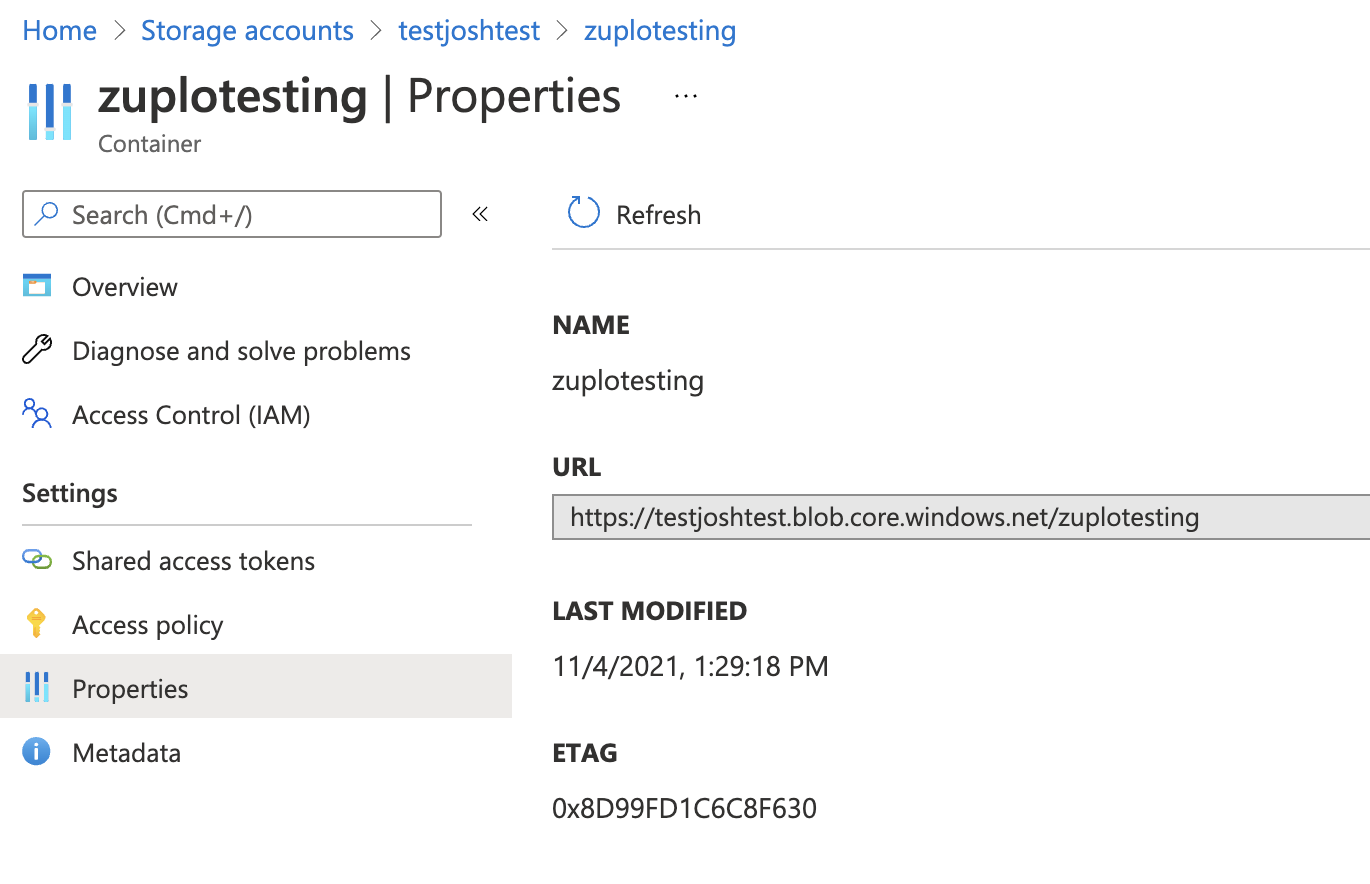
This URL will be the blobPath in our policy options.
Next, we'll need a SAS (Shared Access Secret) to authenticate with Azure. You
can generate one of these on the Shared access tokens tab.
Note, you should minimize the permissions - and select only the Create
permission. Choose a sensible start and expiration time for your token. Note, we
don't recommend restricting IP addresses because Zuplo runs at the edge in over
200 data-centers world-wide.
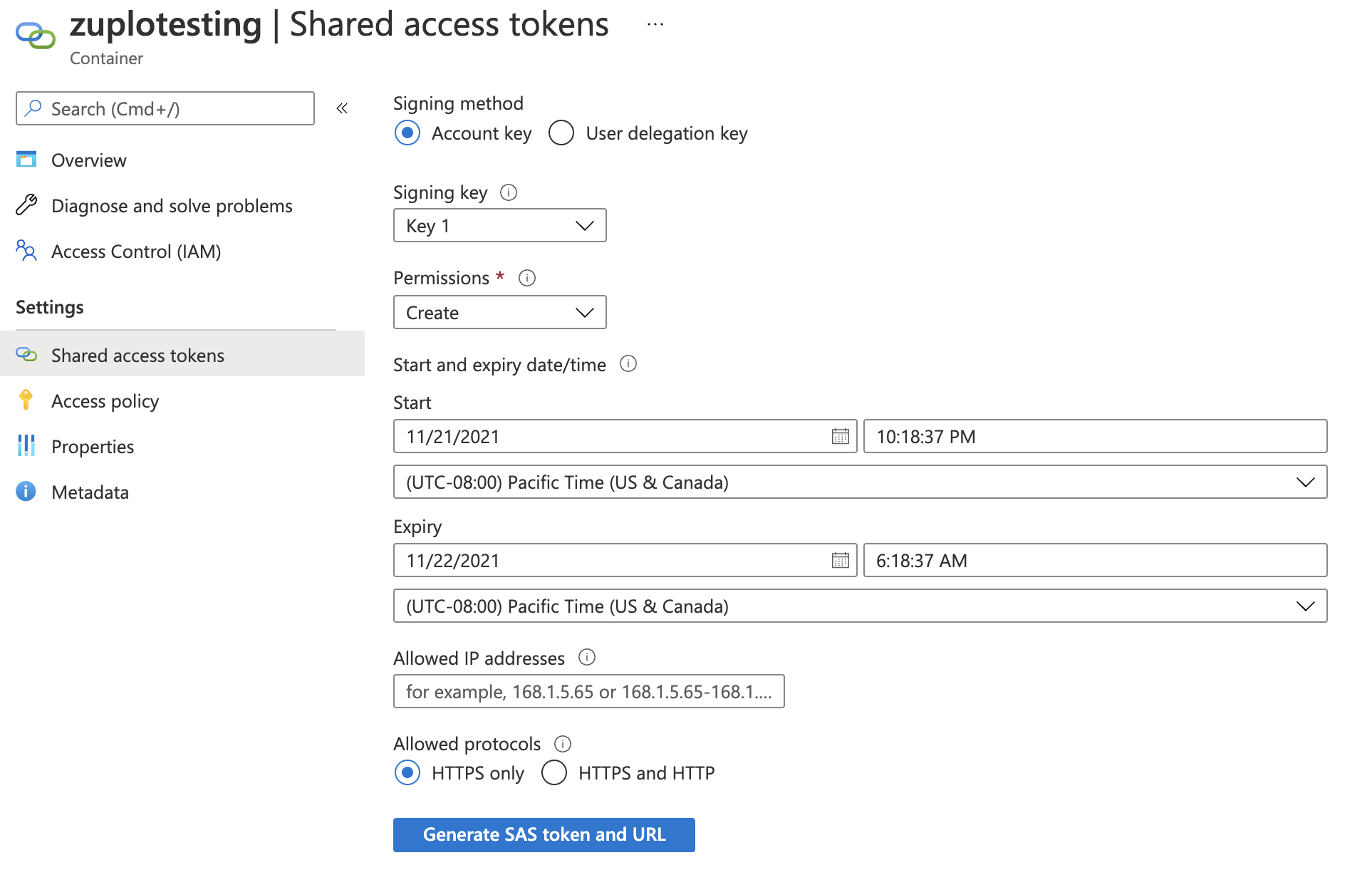
Then generate your SAS token - copy the token (not the URL) to the clipboard and
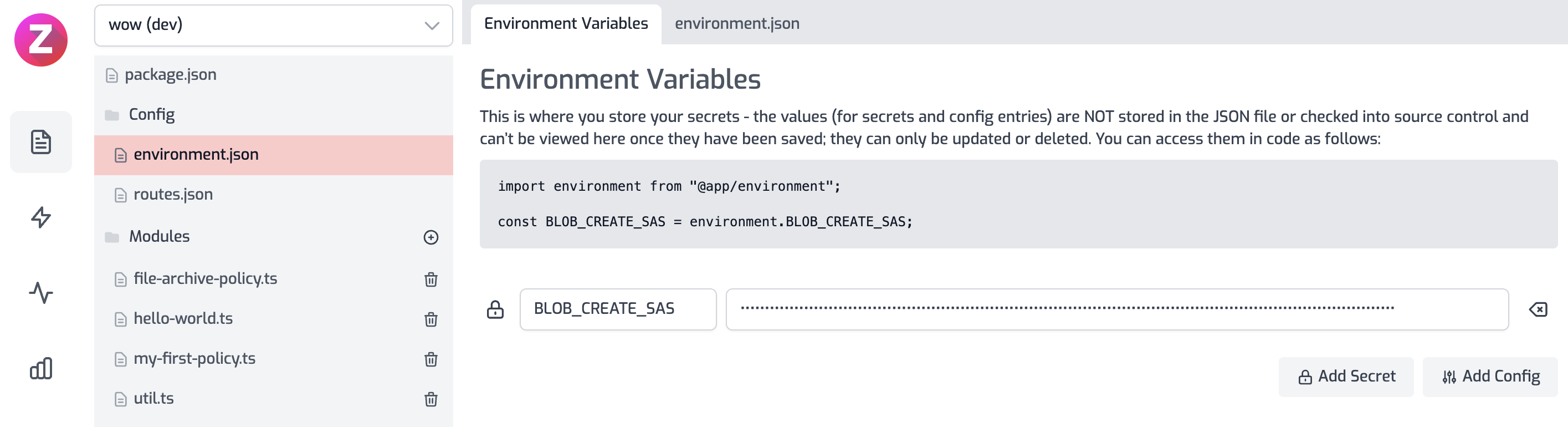
enter it into a new environment variable in your API called BLOB_CREATE_SAS.
You'll need another environment variable called BLOB_CONTAINER_PATH.
Read more about how policies work